Reasons to Take a Physical Security Assessment of Your Office
When we talk IT security most companies just think about protecting themselves against external cyber security threats. But what most companies don't realize is that within your business walls many cubicle walls are leaving your firm susceptible to network security hacks.
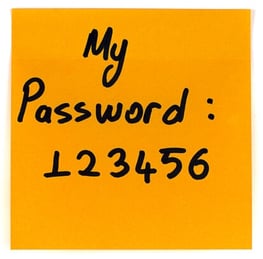
RKL's Technology Services team recently conducted a network/security assessment of a client and the first phase of the assessment included the physical entry to employees offices and an attempt at accessing the businesses network. Upon the completion of the vulnerability assessment, it was discovered that a number of cubicles and offices had sticky/post-it notes containing network and application logins. A number of the logins posted were for externally hosted applications, wireless network passwords, and even client passwords. As a result of this information being made readily available, we were able to use this information to make attempts to access the companies network and their externally hosted applications.
Protecting Against Physical Security Threats
To protect against internal network security threats we recommend your IT team does a physical security risk assessment of your employee's workspaces. Make it a policy to have everyone remove all sticky/post-it notes that contain any type of account logins, wireless passcodes, and client login information. This includes any notes or pieces of paper stored under keyboards and desk drawers.
Your IT Department should conduct a regular internal audit to review all office workspaces to ensure the policy is being followed. It is important to remind everyone that passwords are a critical component of information security. In order to ensure the security and confidentiality of client's information, you should have 100% compliance.
Have Questions or Need Help?
 RKL eSolutions offers Technology Services including IT/Cyber Security Assessments. Click below to get in touch with us here at RKL eSolutions if you have questions about assessing internal and external threats to your company.
RKL eSolutions offers Technology Services including IT/Cyber Security Assessments. Click below to get in touch with us here at RKL eSolutions if you have questions about assessing internal and external threats to your company.
Contact Us!