Ever had a run in with a ransomware virus? A ransomware virus such as CryptoWall is a virus that will encrypt files on your local computer then move on to any mapped drive letters. It can be “caught” as easily as clicking on a web .pdf. The first sign of a problem, if you’re paying attention, is that your hard drive light will be on constantly and your computer will seem slow.
Cryptowall Trojan Ransomware Virus
My first experience with Cryptowall came when I received a call for help and the IT guy said that he thought there was a problem, users had trouble opening files and the files HELP_DECRYPT.HTML, HELP_DECRYPT.PNG, HELP_DECRYPT.TXT AND HELP_DECRYPT.URL were appearing in all their folders. After a quick Google search I told him it looked like he had the CryptoWall virus and that the offending workstation should be immediately disconnected. He said he didn’t know which one it was and I told him that the offending computer will be slow and have those files in their folders on drive c:. He mentioned his computer had been running slowly and took a look and it turned out that it was his own computer doing the encrypting. A fast way to determine the culprit is to go to a folder with telltale HELP_DECRYPT.* files and do the following:
- Choose View/Details
- Right click on the information bar at the top of the file list
![]()
- Choose more
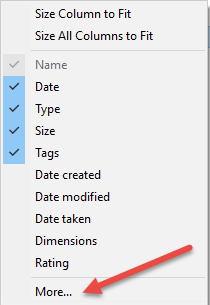
- Scroll down and choose Owner.
This will show which user is doing the encrypting. Once we narrowed down that it was him and only him we had to deal with the encrypted data.
What it does
CyptoWall is very good at what it does, when you’re hit with it there are only two choices, restore from backup (possibly from Shadow Copy) and unencrypt the files. Another thing CryptoWall is good at is pointing out the failings of your backup system. In the case of the customer he was using many manually selected folders. In the case of his backup when you select some folders and not others, folders created after those choices aren’t automatically selected which left him thinking he had complete backups when he did not. Unfortunately, in this case, a huge store of critical data was not backed up.
Paying the Ransom
Not having this data would almost certainly have meant his job, after some brief discussions it was determined that we would pay the ransom. The above mentioned files each contain instructions to go to a customized web page that tells you how to pay the ransom with bitcoin and the bitcoin address to send it to. As it happened I was already in possession of the necessary amount of bitcoin and sent it to the address. If you do not already own bitcoin getting it can be difficult and time consuming which may be frustrating since the ransom doubles after a certain amount of time. Hopefully you already know someone to help you with the procurement since that in itself could be an entire blog.
After paying the ransom a few hours went by and the web site then provided a link to download the public key, private key, and unencryption software to unencrypt the files. They actually have tech support and I’m told that their support is very good, I suppose it has to be if they want to continue to get $500 from each of their “clients”. We ran the unencryption against the files and, as promised, nearly all of them were back in their original condition though there were a few corrupted files which conceivably could have been corrupted before the virus.
Periodically Backup
As a sanity check a coworker was at an IT Roundtable and asked for a show of hands from anybody whom has had to deal with CryptoWall. Out of 40ish people all but two hands went up. The ubiquity of this virus and the severity of it demand proactive action. The single best thing you can do is review your backups periodically to ensure you are backing up what you think you are, and knowing you can restore everything of importance. Sending money to an unknown entity is a difficult pill to swallow.
RKL eSolutions, helps clients in a wide range of industries implement network and information systems infrastructure with an eye to security and accuracy. Contact RKL eSolutions today to find out how they can help your business tackle its IT challenges.



